The Engine of the Modern World
Why this matters: IT powers nearly every aspect of modern life and business. Understanding its foundation is essential for navigating today's digital landscape securely and efficiently.
To understand the importance of IT, let's start with an experiment. Try turning off the essential tools you rely on every day.
Imagine a day without these tools. That reality is a world without Information Technology. IT is the practice of using computers, networks, and storage devices to create, process, store, and exchange electronic data.
The IT Trinity: Core Components
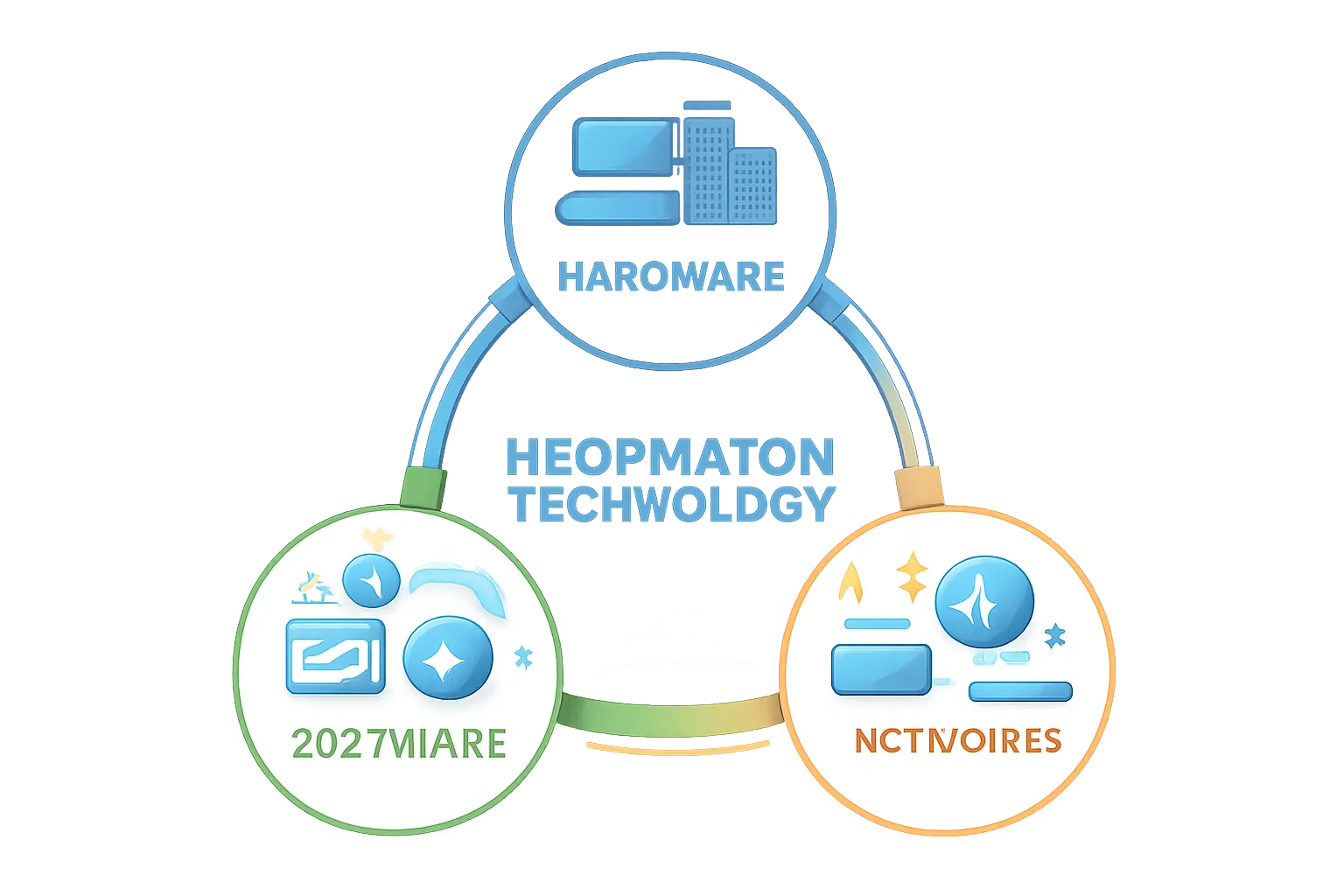
Information Technology infrastructure is built upon three foundational pillars. They work together seamlessly to allow data to flow.
Hardware
The physical equipment. Includes servers, laptops, routers, and storage drives.
Software
The logical programs and operating systems that tell the hardware what to do.
Networks
The connections (wired or wireless) that link hardware together to share data.
Think of it like a restaurant: The building and kitchen equipment are the Hardware. The recipes and procedures are the Software. The waiters moving food from the kitchen to the tables represent the Network.
Knowledge Check
Which component of IT infrastructure is responsible for physically storing data and running applications?
Networks: The Digital Highways

A computer on its own is a powerful tool, but a network of computers is a global force. Networks are categorized by their geographic scale.
LAN (Local Area Network)
Connects devices in a limited area like a single home, office building, or school campus. It allows local devices to share printers and local files quickly.
WAN (Wide Area Network)
Spans large geographic distances, connecting multiple LANs together. The Internet is the world's largest public WAN.
Without networks, data would be isolated on individual devices, making modern communication and cloud computing impossible.
Cybersecurity: The Digital Shields

With great connectivity comes great vulnerability. Because networks allow devices to communicate globally, they also expose systems to digital threats.
Cybersecurity is the practice of protecting systems, networks, and programs from digital attacks. These attacks usually aim to access, change, or destroy sensitive information.
- Firewalls: Act as security guards, filtering incoming and outgoing network traffic based on security rules.
- Encryption: Scrambles data into unreadable text so that even if it's intercepted, it cannot be read without a key.
- Access Controls: Passwords and multi-factor authentication (MFA) ensure only authorized users access the system.
Knowledge Check
What is the primary function of a firewall in an IT infrastructure?
Key Takeaways
- IT defined: The use of hardware, software, and networks to manage electronic data.
- Three Pillars: Hardware (physical), Software (logical), and Networks (connectivity).
- Scales of Networks: LANs handle local, limited-area connections, while WANs handle broad, geographic connections.
- Cybersecurity: An essential layer that protects systems, networks, and data from unauthorized access and attacks.
You are now ready to take the final assessment to complete this protocol.
Final Assessment
Welcome to the final assessment for the Fundamentals of Information Technology.
- There are 3 multiple-choice questions.
- You need a score of 80% or higher to pass and earn your certificate.
- Take your time. Once you select an answer, you can proceed to the next question.
Click "Next" to begin.
Question 1 of 3
Which statement best defines the core scope of Information Technology?
Question 2 of 3
Which statement accurately distinguishes a LAN from a WAN?
Question 3 of 3
What is the primary role of cybersecurity within an IT infrastructure?
Protocol Results
Your final score is: